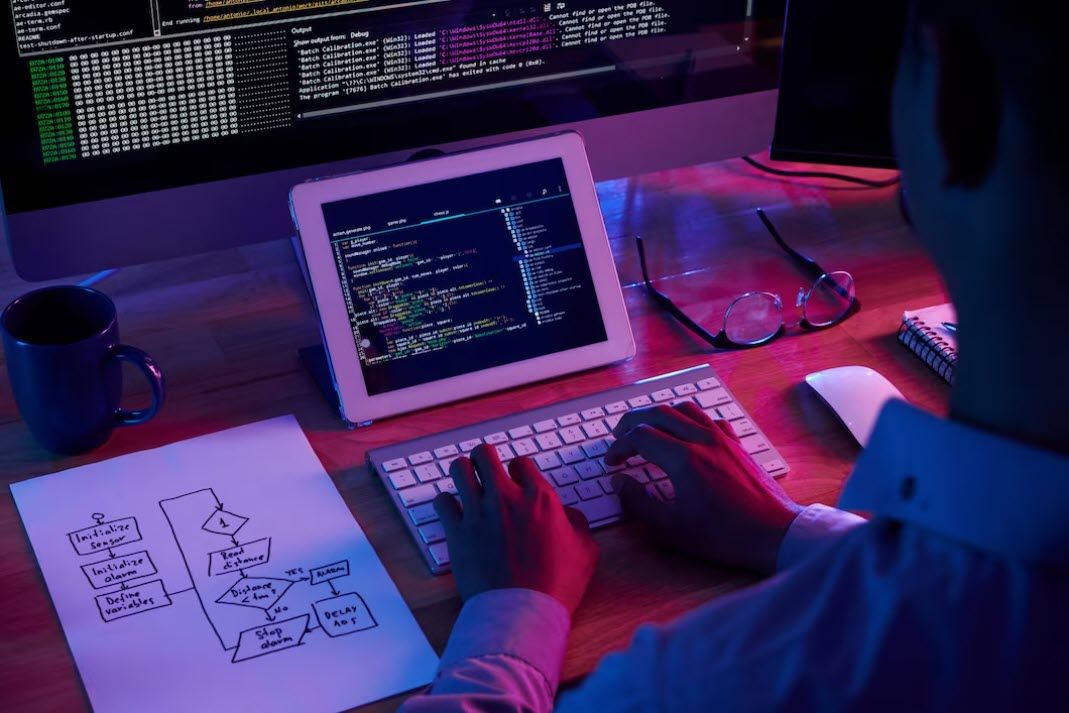
What is Encryption and Why is it Essential?
Encryption is the process of converting readable data into an encoded format that can only be accessed or decrypted by authorized users. It is an essential tool in protecting sensitive information from cyber threats, ensuring data integrity, and maintaining confidentiality in online communications.
Read More